BUUCTF 每日打卡 2021-7-18
引言
早点更完,学ML去
[GUET-CTF2019]NO SOS
给了个附件: ![在这里插入图片描述]() 摩斯电码? 但是又没有分隔符 还有这些长短不一的点和横是怎么回事 NO SOS?是没有'S'和'O'的意思吗? 没想法,找wp 原来 NO SOS 是暗示这不是摩尔斯电码,要把'.'和'-'分别替换成'a'和'b'搞成培根密码(反正我是想不到的) 解密代码如下:
摩斯电码? 但是又没有分隔符 还有这些长短不一的点和横是怎么回事 NO SOS?是没有'S'和'O'的意思吗? 没想法,找wp 原来 NO SOS 是暗示这不是摩尔斯电码,要把'.'和'-'分别替换成'a'和'b'搞成培根密码(反正我是想不到的) 解密代码如下:
1
2
3
4
| c = '..-.-.-.–…….–..-…-..-…–.-.-….-..-..–.-.-..-.-..—-'.replace('…', '...').replace('—', '---').replace('–', '--')
print(c.replace('.', 'a').replace('-', 'b'))
print(c.replace('.', 'b').replace('-', 'a'))
|
要记得把不同长度换成相同长度的 然后找了个在线工具解密 其中第一个是正解 结果如下: ![在这里插入图片描述]()
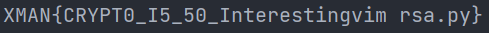
[QCTF2018]Xman-RSA
这题可以说是相当爱折腾 一上来给了四个附件 ![在这里插入图片描述]() 前三个文件都是密文 第四个文件是加密的加密程序(啊这)
前三个文件都是密文 第四个文件是加密的加密程序(啊这) 1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
| gqhb jbkl2 pbkhqw pt_kqpbd
gqhb ht pbkhqw zqreahb
pbkhqw urtd64
adg ulwdt_wh_ezb(u):
qdwzqe pew(u.dexhad('mdi'), 16)
adg ezb_wh_ulwdt(e):
u = mdi(e)[2:-1]
u = '0' + u pg yde(u)%2 == 1 dytd u
qdwzqe u.adxhad('mdi')
adg jdw_r_kqpbd(y):
qreahb_tdda = zqreahb(y)
ezb = ulwdt_wh_ezb(qreahb_tdda)
fmpyd Tqzd:
pg pt_kqpbd(ezb):
uqdrv
ezb+=1
qdwzqe ezb
adg dexqlkw(t, d, e):
k = ulwdt_wh_ezb(t)
k = khf(k, d, e)
qdwzqe ezb_wh_ulwdt(k).dexhad('mdi')
adg tdkrqrwd(e):
k = e % 4
w = (k*k) % 4
qdwzqe w == 1
g = hkde('gyrj.wiw', 'q')
gyrj = g.qdra()
btj1 = ""
btj2 = ""
ghq p pe qrejd(yde(gyrj)):
pg tdkrqrwd(p):
btj2 += gyrj[p]
dytd:
btj1 += gyrj[p]
k1 = jdw_r_kqpbd(128)
k2 = jdw_r_kqpbd(128)
k3 = jdw_r_kqpbd(128)
e1 = k1*k2
e2 = k1*k3
d = 0i1001
x1 = dexqlkw(btj1, d, e1)
x2 = dexqlkw(btj2, d, e2)
kqpew(x1)
kqpew(x2)
d1 = 0i1001
d2 = 0i101
k4 = jdw_r_kqpbd(128)
k5 = jdw_r_kqpbd(128)
e3 = k4*k5
x1 = ezb_wh_ulwdt(khf(e1, d1, e3)).dexhad('mdi')
x2 = ezb_wh_ulwdt(khf(e1, d2, e3)).dexhad('mdi')
kqpew(x1)
kqpew(x2)
kqpew(urtd64.u64dexhad(ezb_wh_ulwdt(e2)))
kqpew(urtd64.u64dexhad(ezb_wh_ulwdt(e3)))
|
1
2
3
4
5
6
7
8
9
10
11
12
| with open('encryption.encrypted', 'r') as f:
encrypt = f.read()
table = ['r', 'u', 'x', 'a', 'd', 'g', 'j', 'm', 'p', ' ', 'v', 'y', 'b', 'e', 'h', 'k', ' ', 'q', 't', 'w', 'z', ' ', 'f', 'i', 'l', ' ']
dict = {}
for i in range(len(table)):
if table[i] != ' ':
dict[table[i]] = chr(ord('a')+i)
else:
dict[table[i]] = ' '
print(encrypt.translate(str.maketrans(dict)))
|
原加密程序如下:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
| from gmpy2 import is_prime
from os import urandom
import base64
def bytes_to_num(b):
return int(b.encode('hex'), 16)
def num_to_bytes(n):
b = hex(n)[2:-1]
b = '0' + b if len(b) % 2 == 1 else b
return b.decode('hex')
def get_a_prime(l):
random_seed = urandom(l)
num = bytes_to_num(random_seed)
while True:
if is_prime(num):
break
num += 1
return num
def encrypt(s, e, n):
p = bytes_to_num(s)
p = pow(p, e, n)
return num_to_bytes(p).encode('hex')
def separate(n):
p = n % 4
t = (p * p) % 4
return t == 1
f = open('flag.txt', 'r')
flag = f.read()
msg1 = ""
msg2 = ""
for i in range(len(flag)):
if separate(i):
msg2 += flag[i]
else:
msg1 += flag[i]
p1 = get_a_prime(128)
p2 = get_a_prime(128)
p3 = get_a_prime(128)
n1 = p1 * p2
n2 = p1 * p3
e = 0x1001
c1 = encrypt(msg1, e, n1)
c2 = encrypt(msg2, e, n2)
print(c1)
print(c2)
e1 = 0x1001
e2 = 0x101
p4 = get_a_prime(128)
p5 = get_a_prime(128)
n3 = p4 * p5
c1 = num_to_bytes(pow(n1, e1, n3)).encode('hex')
c2 = num_to_bytes(pow(n1, e2, n3)).encode('hex')
print(c1)
print(c2)
print(base64.b64encode(num_to_bytes(n2)))
print(base64.b64encode(num_to_bytes(n3)))
|
其实就是先把flag奇偶位置分开分别用n1,n2加密,然后又把加密用的n1再用n3加密,再把加密n1用的n3和之前的n2用base64加密(对,就是套娃) 还原n2,n3是简单的,其中n2可以直接爆破,而n3不行 但容易发现加密n1得到两个密文,用的都是n3,所以可以用共模攻击解出n1 又发现n1也可以爆破 最后就是基本的RSA解密了 解密出msg1和msg2后拼接就是flag 解密代码如下:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
| import base64
from Crypto.Util.number import *
import gmpy2
def decrypt(c, e, p, q):
phi = (p-1)*(q-1)
d = inverse(e, phi)
m = pow(c, d, p*q)
return m
mc1 = '1240198b148089290e375b999569f0d53c32d356b2e95f5acee070f016b3bef243d0b5e46d9ad7aa7dfe2f21bda920d0ac7ce7b1e48f22b2de410c6f391ce7c4347c65ffc9704ecb3068005e9f35cbbb7b27e0f7a18f4f42ae572d77aaa3ee189418d6a07bab7d93beaa365c98349d8599eb68d21313795f380f05f5b3dfdc6272635ede1f83d308c0fdb2baf444b9ee138132d0d532c3c7e60efb25b9bf9cb62dba9833aa3706344229bd6045f0877661a073b6deef2763452d0ad7ab3404ba494b93fd6dfdf4c28e4fe83a72884a99ddf15ca030ace978f2da87b79b4f504f1d15b5b96c654f6cd5179b72ed5f84d3a16a8f0d5bf6774e7fd98d27bf3c9839'
mc2 = '129d5d4ab3f9e8017d4e6761702467bbeb1b884b6c4f8ff397d078a8c41186a3d52977fa2307d5b6a0ad01fedfc3ba7b70f776ba3790a43444fb954e5afd64b1a3abeb6507cf70a5eb44678a886adf81cb4848a35afb4db7cd7818f566c7e6e2911f5ababdbdd2d4ff9825827e58d48d5466e021a64599b3e867840c07e29582961f81643df07f678a61a9f9027ebd34094e272dfbdc4619fa0ac60f0189af785df77e7ec784e086cf692a7bf7113a7fb8446a65efa8b431c6f72c14bcfa49c9b491fb1d87f2570059e0f13166a85bb555b40549f45f04bc5dbd09d8b858a5382be6497d88197ffb86381085756365bd757ec3cdfa8a77ba1728ec2de596c5ab'
n1c1 = '2639c28e3609a4a8c953cca9c326e8e062756305ae8aee6efcd346458aade3ee8c2106ab9dfe5f470804f366af738aa493fd2dc26cb249a922e121287f3eddec0ed8dea89747dc57aed7cd2089d75c23a69bf601f490a64f73f6a583081ae3a7ed52238c13a95d3322065adba9053ee5b12f1de1873dbad9fbf4a50a2f58088df0fddfe2ed8ca1118c81268c8c0fd5572494276f4e48b5eb424f116e6f5e9d66da1b6b3a8f102539b690c1636e82906a46f3c5434d5b04ed7938861f8d453908970eccef07bf13f723d6fdd26a61be8b9462d0ddfbedc91886df194ea022e56c1780aa6c76b9f1c7d5ea743dc75cec3c805324e90ea577fa396a1effdafa3090'
n1c2 = '42ff1157363d9cd10da64eb4382b6457ebb740dbef40ade9b24a174d0145adaa0115d86aa2fc2a41257f2b62486eaebb655925dac78dd8d13ab405aef5b8b8f9830094c712193500db49fb801e1368c73f88f6d8533c99c8e7259f8b9d1c926c47215ed327114f235ba8c873af7a0052aa2d32c52880db55c5615e5a1793b690c37efdd5e503f717bb8de716303e4d6c4116f62d81be852c5d36ef282a958d8c82cf3b458dcc8191dcc7b490f227d1562b1d57fbcf7bf4b78a5d90cd385fd79c8ca4688e7d62b3204aeaf9692ba4d4e44875eaa63642775846434f9ce51d138ca702d907849823b1e86896e4ea6223f93fae68b026cfe5fa5a665569a9e3948a'
n2 = 'PVNHb2BfGAnmxLrbKhgsYXRwWIL9eOj6K0s3I0slKHCTXTAUtZh3T0r+RoSlhpO3+77AY8P7WETYz2Jzuv5FV/mMODoFrM5fMyQsNt90VynR6J3Jv+fnPJPsm2hJ1Fqt7EKaVRwCbt6a4BdcRoHJsYN/+eh7k/X+FL5XM7viyvQxyFawQrhSV79FIoX6xfjtGW+uAeVF7DScRcl49dlwODhFD7SeLqzoYDJPIQS+VSb3YtvrDgdV+EhuS1bfWvkkXRijlJEpLrgWYmMdfsYX8u/+Ylf5xcBGn3hv1YhQrBCg77AHuUF2w/gJ/ADHFiMcH3ux3nqOsuwnbGSr7jA6Cw=='
n3 = 'TmNVbWUhCXR1od3gBpM+HGMKK/4ErfIKITxomQ/QmNCZlzmmsNyPXQBiMEeUB8udO7lWjQTYGjD6k21xjThHTNDG4z6C2cNNPz73VIaNTGz0hrh6CmqDowFbyrk+rv53QSkVKPa8EZnFKwGz9B3zXimm1D+01cov7V/ZDfrHrEjsDkgK4ZlrQxPpZAPl+yqGlRK8soBKhY/PF3/GjbquRYeYKbagpUmWOhLnF4/+DP33ve/EpaSAPirZXzf8hyatL4/5tAZ0uNq9W6T4GoMG+N7aS2GeyUA2sLJMHymW4cFK5l5kUvjslRdXOHTmz5eHxqIV6TmSBQRgovUijlNamQ=='
e = int('0x1001', 16)
e1 = int('0x1001', 16)
e2 = int('0x101', 16)
mc1 = int(mc1, 16)
mc2 = int(mc2, 16)
n1c1 = int(n1c1, 16)
n1c2 = int(n1c2, 16)
n2 = bytes_to_long(base64.b64decode(n2))
n3 = bytes_to_long(base64.b64decode(n3))
print(n2, n3)
gcd, s, t = gmpy2.gcdext(e1, e2)
if s < 0:
s = -s
n1c1 = gmpy2.invert(n1c1, n3)
if t < 0:
t = -t
n1c2 = gmpy2.invert(n1c2, n3)
n1 = gmpy2.powmod(n1c1, s, n3) * gmpy2.powmod(n1c2, t, n3) % n3
print(n1)
p1 = 36503560711222200347745635238792106713920033958622200829092748503591270659903081394620276506325026411074230626397319741508641600002903305233380003999170571805545704321579972221393658587490213987917997698711182322920804807669281318998024155277432216030985270653843416557319053811218180174081048812060180634801
q1 = 68475150402136550069561649755295544963289030785101058202360554598728892273874900512013972536010281921862638482624050145776516868431210229550944533343142576416459199101144902197593841367980791503251475193609136925280837184839979646652186999511796418448787979170775450657311911945185202715164053596280658868979
p2 = 68475150402136550069561649755295544963289030785101058202360554598728892273874900512013972536010281921862638482624050145776516868431210229550944533343142576416459199101144902197593841367980791503251475193609136925280837184839979646652186999511796418448787979170775450657311911945185202715164053596280658868979
q2 = 113057116110640629442838729892384636071708596904428483152114609685936140664770589059214780753000125747653792221591510804947737833483206498631262985233023673075253476613965561679900695245558177430781375269136603105651856671527157586176048122119973067362460787539110922411635014408169669810929828500304139655817
msg1 = long_to_bytes(decrypt(mc1, e, p1, q1)).decode()
msg2 = long_to_bytes(decrypt(mc2, e, p2, q2)).decode()
flag = ''
for i in range(len(msg1)+len(msg2)):
if i % 2 == 1:
flag += msg2[(i-1)//2]
else:
flag += msg1[i//2]
print(flag)
|
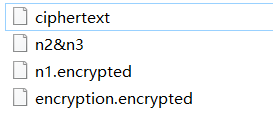
结果为: ![在这里插入图片描述]()
结语
希望继续坚持
 摩斯电码? 但是又没有分隔符 还有这些长短不一的点和横是怎么回事 NO SOS?是没有'S'和'O'的意思吗? 没想法,找wp 原来 NO SOS 是暗示这不是摩尔斯电码,要把'.'和'-'分别替换成'a'和'b'搞成培根密码(反正我是想不到的) 解密代码如下:
摩斯电码? 但是又没有分隔符 还有这些长短不一的点和横是怎么回事 NO SOS?是没有'S'和'O'的意思吗? 没想法,找wp 原来 NO SOS 是暗示这不是摩尔斯电码,要把'.'和'-'分别替换成'a'和'b'搞成培根密码(反正我是想不到的) 解密代码如下:
 前三个文件都是密文 第四个文件是加密的加密程序(啊这)
前三个文件都是密文 第四个文件是加密的加密程序(啊这)