BUUCTF 每日打卡 2021-4-15
引言
今天也是元气满满的一天(打哈欠)
childRSA
题目给了 n和c 照例碰运气爆破 n:  啊这 真让我爆破出来了 然后就是 RSA 常规操作 代码如下:
啊这 真让我爆破出来了 然后就是 RSA 常规操作 代码如下: 1
2
3
4
5
6
7
8from Crypto.Util.number import *
# p, q, c, n
e = int('0x10001', 16)
phi = (p-1)*(q-1)
d = inverse(e, phi)
m = pow(c, d, n)
print(long_to_bytes(m))
bbbbbbrsa
附件 python2 加密代码: 1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32from base64 import b64encode as b32encode
from gmpy2 import invert,gcd,iroot
from Crypto.Util.number import *
from binascii import a2b_hex,b2a_hex
import random
flag = "******************************"
nbit = 128
p = getPrime(nbit)
q = getPrime(nbit)
n = p*q
print p
print n
phi = (p-1)*(q-1)
e = random.randint(50000,70000)
while True:
if gcd(e,phi) == 1:
break;
else:
e -= 1;
c = pow(int(b2a_hex(flag),16),e,n)
print b32encode(str(c))[::-1]
# 2373740699529364991763589324200093466206785561836101840381622237225512234632
根据加密代码,c 经过了 base64 加密并且倒序输出了 为了保险起见,还是先解码给出的 c 代码如下: 1
2
3
4
5
6
7
8
9
10import base64
import math
from Crypto.Util.number import *
c = '==gMzYDNzIjMxUTNyIzNzIjMyYTM4MDM0gTMwEjNzgTM2UTN4cjNwIjN2QzM5ADMwIDNyMTO4UzM2cTM5kDN2MTOyUTO5YDM0czM3MjM'[::-1]
base64_bytes = c.encode('ascii')
message_bytes = base64.b64decode(base64_bytes)
message = message_bytes.decode('ascii')
print(message)
c = int(message)1
2
3
4
5
6
7
8
9
10
11p = 177077389675257695042507998165006460849
n = 37421829509887796274897162249367329400988647145613325367337968063341372726061
q = n//p
phi = (p-1)*(q-1)
for e in range(50000, 70000):
if math.gcd(e, phi) == 1:
d = inverse(e, phi)
m = str(long_to_bytes(pow(c, d, n)))
if '{' in m and '}' in m:
print(m)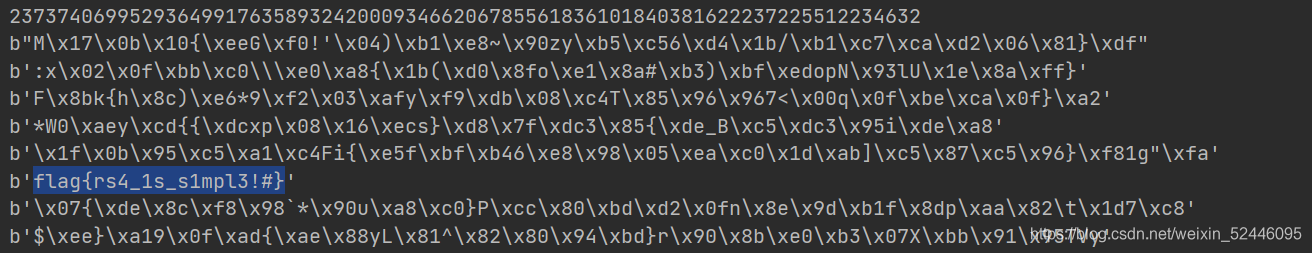
结语
啊。。。好像也没什么好说的 希望继续坚持